Complete Guide On AOL Header Analysis
Email headers are the part of emails, which contains the complete information about the email that includes date, subject, information, sender, receiver, etc. All the email applications usually display only the small portions of the email header, which are beneficial for users. The complete email header AOL mail mainly contains the code and data, which helps email applications to detect, sort as well as deliver mail. Even the information is also used in the headers that help to filter and block specific senders, such spammers. This is one of the reasons for most of the business users utilize ESP (Email Service Provider) with a good reputation and ISPs (Internet Service Providers) that helps to safeguard that the Email Message Headers are up to snuff, and can be recognized as belonging to legitimate emails. There are numerous of email application available in the online market. Out of which, one such email application is AOL (America Online). It is considered as an early Internet pioneer that offers various Internet services including dial-up Internet access, email, as well as instant messaging. However, by the passing of time now, AOL was purchased by Verizon in 2015. In the following section, we will discuss the complete AOL header analysis.
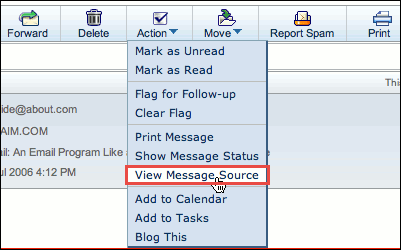
Extraction of AOL Email Header Information
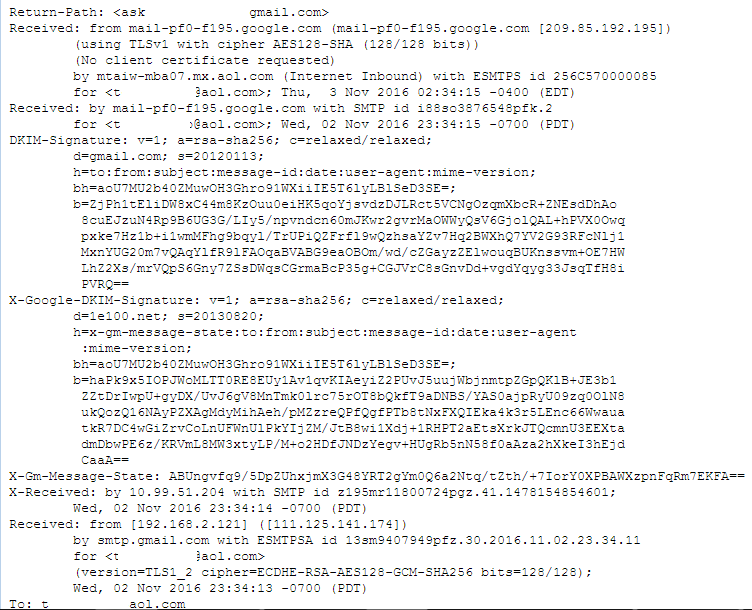
Return-Path: Each mail message has hidden field, which is known as "Return-Path" address. It is also known as "bounce address" or "envelope sender address". It is the address of a message from where it really came from. It is the address to which gives notices of any undeliverable message that are sent. When the users send mail from a script on the servers, the Return-Path will be automatically set a value, which by default works with our servers. However, it is likely for scripts to be written to override the default Return-Path. One cannot send any messages by using a Return-Path address of domain names, which are not hosted, such as aol.com. For this, users need to create scripts and do not set a custom Return-Path address unless it ends via a domain name.
Receiver: This service covers the field of headers that are received in each message procedure. It contains the sender's IP address and complete details of the Transport Layer Security (TLS). This means that there is safe and secure spread from sending server from which particular server the message is deal with. The digital signature is added, which let the system make difference between the NDRs, it is the result from spammers by utilizing forged address and timestamp. The mail server may add the complete details to the header, which shows that the mail was received via TLS from service of security.
DKIM-Signature: DKIM is mail security standard, which is designed to make sure that messages are not altered in transit between the servers of sending and recipient. It utilizes public-key cryptography to sign email via a private key as it leaves sending server. Receiver servers can then, utilize a public key published to a domain's DNS to confirm the source of the message, and body of the message has not altered during transit. Once the hash is made and the private key is verified via public key by the recipient server, the message passes DKIM and is considered as authentic.
X-Google-DKIM-Signature: There are various authentications, Google itself adds as X-Google-DKIM Signature field in the mail header to increase authentication of signatures. The subsequent fields are located within the field indicates that the information related to digital signatures are completely encoding.
X Received: The server adds X-received header field in mail addresses for the indication of non-standard header information. It specifies the following information:
- The IP address of the server that received message
- SMTP ID for server
- Exact date as well as time when the mail was received
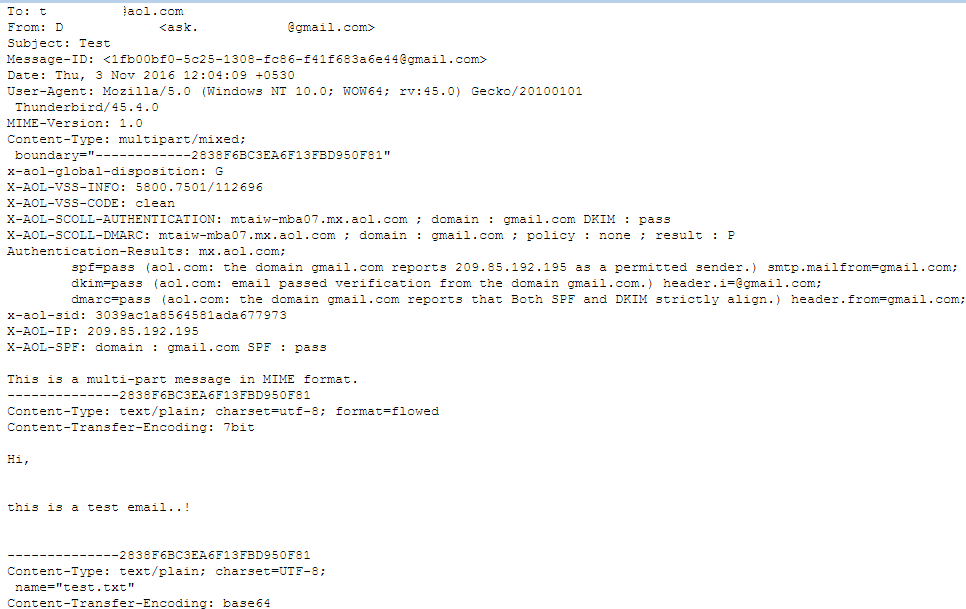
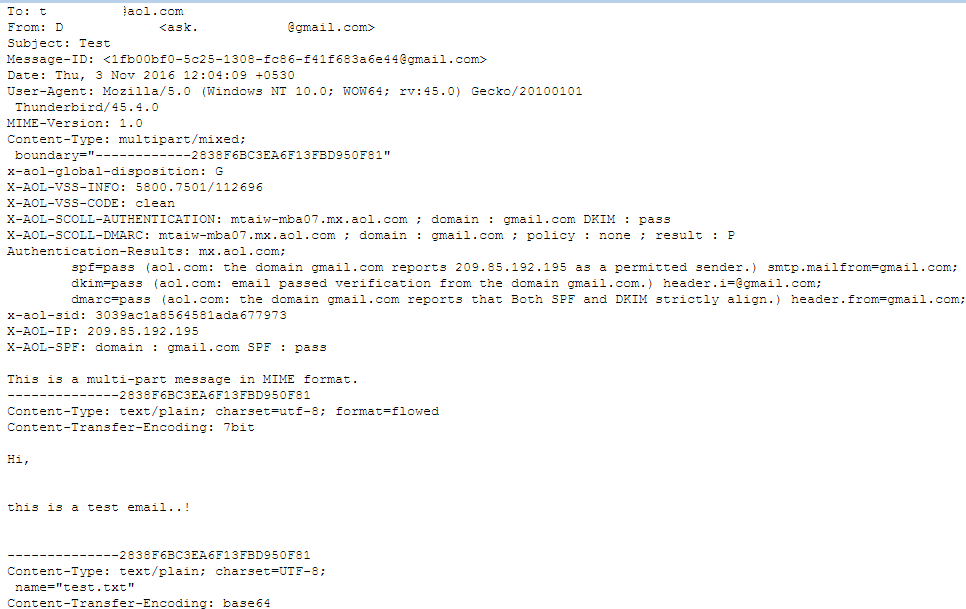
From: This displays to whom the mail is from; however, this can be easily copied. It is the least reliable as well.
Subject: This indicates what the sender placed as a topic of the mail content, which is sent. It offers an idea of what the mail contains actually.
Date: It shows the date and time of mail message, which was composed. It makes easy for user to know the complete and important details about the composed date of the content.
To: It shows to whom the mail message was addressed but may not enclose the receiver's address.
Return-Path: The email address for return-mail is similar as "Reply-To" option in the mail we have. It creates an ease as the user directly replies to their mentioned emails and it makes a kind of conversational method.
Mime-Version: It is the one, which helps to specify the version of the MIME protocol that was used by the sender for sending mail. Similar to other MIME headers, this one is mainly highly ignorable, however; most of the modern email programs will do the right thing with it.
x-AOL- SCOLL- DMARC: DMARC stands for the Domain-based Message Authentication, Reporting, and Conformance is a technical description, which is created by a group of organizations that will help in reducing the potential for mail-based abuse by resolving a couple of long-standing operational, deployment, as well as reporting issues related to protocols of mail authentication.
X-AOL-SPF: The server adds a received-SPF field, which indicates whether the mail message comes from a verified sender or not. It relates techniques for the verification of the sender's identity and forwards only message if the sender is authenticated.